It has been a long time since we posted in this blog. We have been very busy for the past couple of years. But it is time we connect again with our users. iKnode is very much alive and we have been hard at work making it a world class service. The purpose of this post is to give you an update on what we are doing to be complaint with the GDPR.
The General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR) is a European Regulation that focuses on data protection and privacy for all individuals in the European Union, which goes into effect on friday May 25th, 2018. This regulation applies to all companies based in the European Union, but also any companies that processes data belonging to the EU citizens.
As such this regulation applies to Structum, the parent company of iKnode. We have many users which are European Citizens and this fact makes this regulation extremely important to us. At its most basic form the GDPR specifies how personal data should be collected, stored, protected and used. It is intended to put personal information control back in the hands of their owners.
We are committed to protecting and safeguarding your personal data and as part of this commitment, we have updated our Privacy Policy in preparation of the GDPR legislation. Due to the nature of our service, the iKnode family of services do not require changes to be GDPR compliant. There are no changes to the current settings of your account or how your information is processed.
The GDPR introduces the following user rights and how they are addressed:
- Customers can easily request access to their personal information.
Request your personal information here.
- Customers can easily update their personal information to keep it up to that.
All users can change their personal information using the iKnode Web Console, by clicking their name in the top right corner.
- Customer’s data can easily be removed once the information is no longer necessary.
We have a removal policy of 30 days after a customer has cancelled their account with us.
- Customers can request the deletion of their data.
Customers can request the deletion of their data before the 30 days policy is reached by requesting deletion here.
- Customers can easily request that their data be delivered to themselves or a third party.
Request your personal information here.
There are 2 roles considered by the GDPR:
- Data Processor - Processes and Stores the data collected.
- Data Controller - Determines what and why data is collected.
Structum’s role when it refers to the iKnode family of services is a Data Processor. Developers hosting their apps on the iKnode Cloud are a Data Controller. Please review the GDPR Checklist to make sure you are GDPR compliant.
In order to help iKnode developers, we have added a data export feature that will allow you to extract data easily from iKnode to comply with your users right to request their information.
Query Console Export
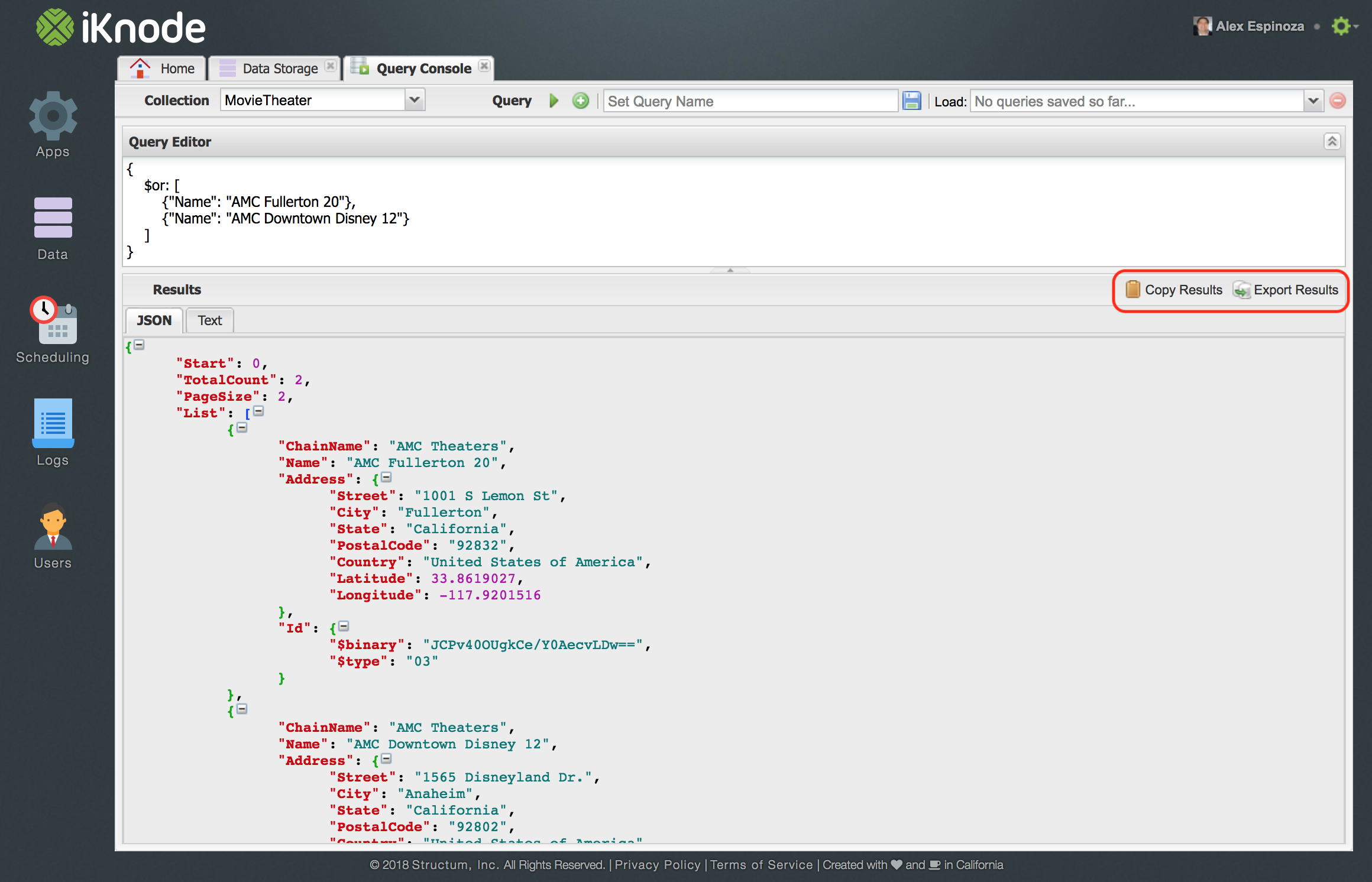 As you can see in the picture above you can type a query on an specific collection and export the results as pure JSON, either by copying it to the clipboard, or by exporting it to a file.
As you can see in the picture above you can type a query on an specific collection and export the results as pure JSON, either by copying it to the clipboard, or by exporting it to a file.
This feature will come in handy when a user of your application requests the data you have collected. You can query by an specific user identifier, and export the data as JSON.
Data Storage Export
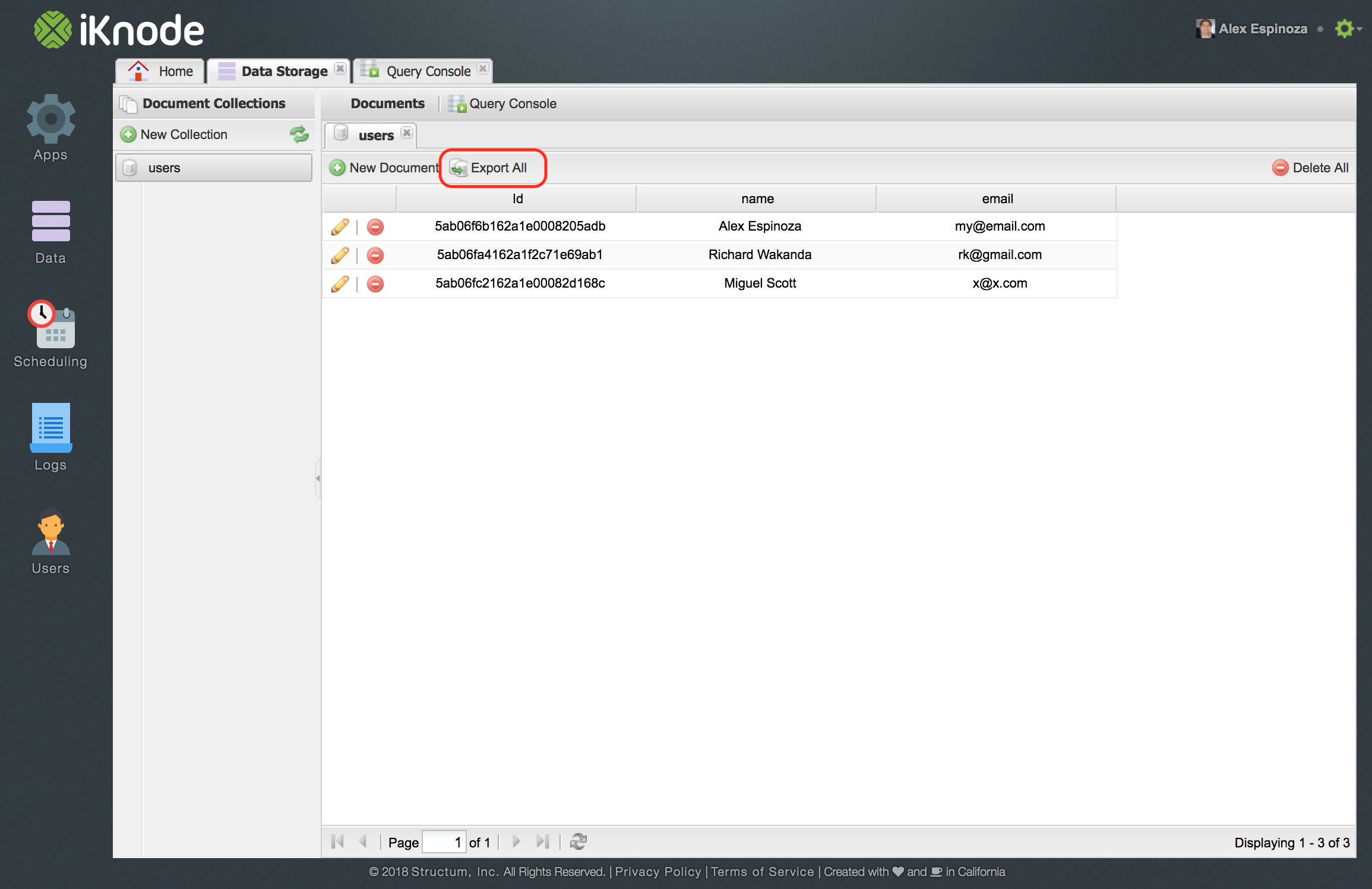 The other way to export your data is by exporting the full collection into JSON. This feature will come in handy if you store all of the data for a user or tenant in a collection. By clicking the “Export All” you will get a file with all of the documents in the collection.
The other way to export your data is by exporting the full collection into JSON. This feature will come in handy if you store all of the data for a user or tenant in a collection. By clicking the “Export All” you will get a file with all of the documents in the collection.
If you have any questions and/or concerns regarding privacy, please do not hestiate to contact us at: privacy@structum.net
To learn more about the GDPR please visit the following sites: